CoreDNS Vulnerability Let Attackers Exhaust Server Memory Via Amplification Attack

A high-severity security vulnerability has been discovered in CoreDNS, one of the most widely used DNS servers in cloud-native environments, particularly within Kubernetes clusters.
The flaw, designated as CVE-2025-47950, allows remote attackers to exhaust server memory through DNS-over-QUIC (DoQ) stream amplification attacks, potentially causing complete service outages in containerized environments.
The vulnerability resides in CoreDNS’s server_quic.go implementation, where the DNS-over-QUIC server creates an unlimited number of goroutines for incoming QUIC streams without imposing concurrency controls.
CoreDNS DNS-over-QUIC Vulnerability
This fundamental design flaw enables attackers to exploit the 1:1 stream-to-goroutine mapping model by opening numerous concurrent streams from a single connection point.
The attack vector demonstrates concerning simplicity, requiring no authentication, minimal bandwidth consumption, and low computational resources from the attacker’s perspective.
A remote, unauthenticated adversary can systematically open large volumes of QUIC streams, triggering uncontrolled memory allocation that eventually leads to Out Of Memory (OOM) conditions.
The vulnerability specifically targets deployments with quic:// protocol enabled in the Corefile configuration, making it particularly dangerous for organizations implementing modern DNS-over-QUIC infrastructure for enhanced privacy and performance.
Security researchers have classified this as a high-impact availability vulnerability, with the potential for complete service disruption.
In memory-constrained environments such as Kubernetes pods or containerized deployments, the impact becomes even more severe, as resource limitations can accelerate the progression toward system failure.
The vulnerability discovery is credited to @thevilledev, who not only identified the security flaw but also contributed a high-quality remediation implementation.
| Risk Factors | Details |
| Affected Products | CoreDNS versions <1.12.2 with quic:// enabled in Corefile configuration |
| Impact | High availability loss (OOM kill or service unresponsiveness) in containerized environments |
| Exploit Prerequisites | – QUIC protocol enabled- Network access to CoreDNS QUIC port- No authentication required |
| CVSS Score | 7.5 (High) |
Patch Implementation
CoreDNS version 1.12.2 addresses this critical vulnerability through a comprehensive redesign of the QUIC stream handling mechanism.
The patch introduces two essential mitigation parameters that fundamentally alter the server’s concurrency model.
The max_streams parameter establishes a ceiling of 256 concurrent QUIC streams per connection by default, while worker_pool_size implements a bounded worker pool architecture with 1024 workers for processing incoming streams.
These configuration options are exposed through the enhanced Corefile syntax:
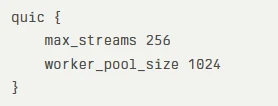
The implementation eliminates the problematic 1:1 stream-to-goroutine relationship, instead utilizing a controlled worker pool that maintains system stability under high-concurrency scenarios.
The default values align with RFC 9250 specifications for DNS over Dedicated QUIC Connections and accommodate typical client behavior patterns observed in production environments.
For organizations unable to immediately upgrade, several temporary workarounds provide interim protection.
Administrators can disable QUIC support entirely by removing or commenting out quic:// blocks in their Corefile configuration.
Additionally, implementing container runtime resource limits helps detect excessive memory consumption patterns, while establishing monitoring systems for QUIC connection anomalies enables early threat detection.
Organizations running affected CoreDNS versions below 1.12.2 should prioritize immediate upgrades, particularly those operating in production environments where DNS availability directly impacts application functionality and user experience.
Live Credential Theft Attack Unmask & Instant Defense – Free Webinar