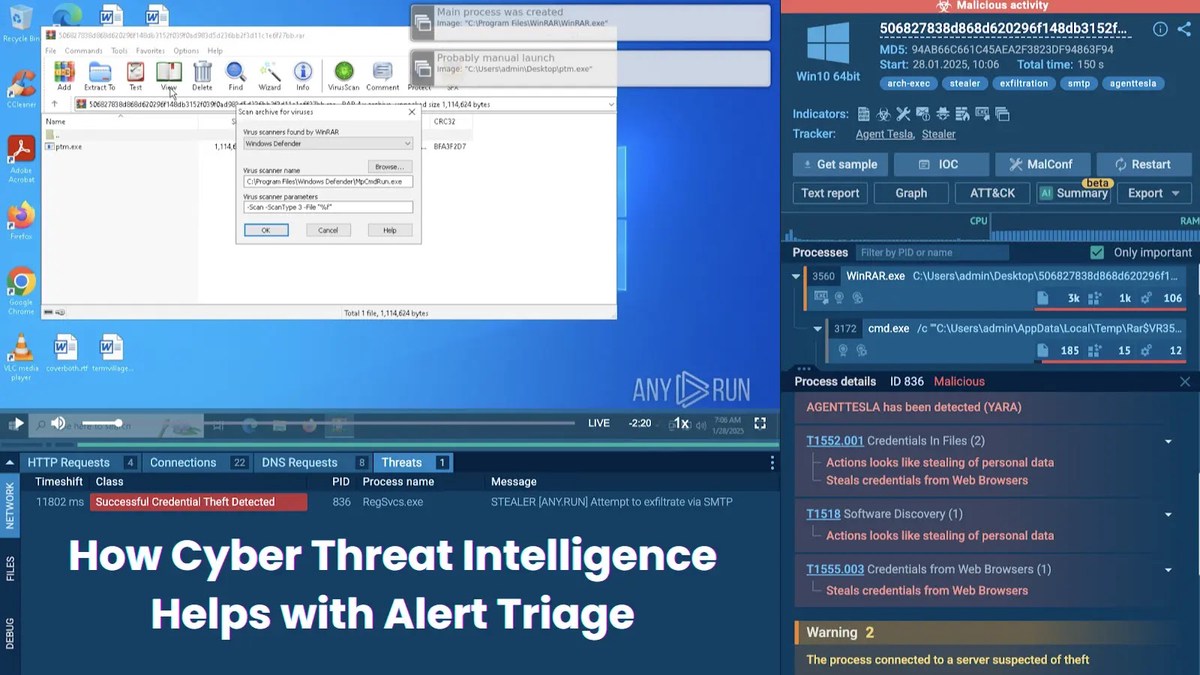
How Cyber Threat Intelligence Helps with Alert Triage
Between threat detection and response, there is a vitally important operation known as alert triage. If not staged properly, it can render the whole SOC’s performance inefficient.
This operation is alert triage — assessing and prioritizing security alerts. SIEM tools, firewalls, endpoint detection solutions and other security systems generate daily a high volume of alerts, and not all of them require any action at all.
Others are more or less critical, and security teams need to define which are which to distribute their resources Alert triage can be decomposed into 2 main tasks:
1. Separating false positives from actual threats;
2. Prioritizing actual threats from low-priority to critical that require immediate action.
What Problems Alert Triage Solves?
Enhances Threat Detection —actual incidents get separated from irrelevant or benign events.
Improves Incident Response — serious threats get escalated to incident response teams efficiently reducing response time and preventing possible attacks.
Leverages Resource Optimization – analysts have their time allocated more effectively and avoid burnout.
Reduces Alert Fatigue — thousands of notifications overload SOC teams daily requiring immediate attention and analysis. Proper triage lets professionals focus on signals that indicate significant risks, cut off noise and avoid desensitization.
Collect threat intelligence on the latest malware and phishing attacks with TI Lookup - Try for Free
How Does Threat Intelligence Facilitate Alert Triage?
Contextual data on threats and alerts helps cyber security teams make informed decisions in several ways
Indicator Enrichment: Real-time context on suspicious IPs, domains, file hashes, and other indicators of compromise (IOCs) lets analysts determine if an alert is related to a known threat actor or malware campaign.
Threat Actor Profiling: Knowing the tactics, techniques, and procedures (TTPs) of adversaries helps to recognize whether an alert is part of a larger attack chain.
Prioritization: Alerts can be prioritized based on current threat landscapes, known vulnerabilities being exploited, or specific targeting by threat actors.
Proactive Defense: Threat intelligence fuels a proactive approach where SOC teams can anticipate incidents, preemptively block malicious infrastructures, adjust their triage processes and response plans accordingly, even before an alert is generated.
Threat Intelligence for Alert Triage: Use Cases
1. An IP traces back to a known stealer
An analyst sees an alert for a suspicious outbound connection to an unknown IP address. Instead of manually investigating the IP, they can search it via Threat Intelligence Lookup from ANY.RUN.
Instantly, they find out that the IP is associated with Agent Tesla, a notorious data stealer.
TI Lookup is a solution for fast initial triage: a powerful search engine that provides fresh contextual data on IOCs and TTPs and helps correlate them with known threats. Over 40 parameters of a search request are available.
Get 50 free requests to try TI Lookup for alert triage - Contact ANY.RUN for a test
In this example, the results of the IP search also contain a list of sandbox tasks with malware sample analysis. They signal that the cybersecurity community had flagged the IP in question as an indicator of a serious threat that has to be instantly dealt with.
Viewing the malware’s behavior in the sandbox lets analysts understand its mechanics and gather additional IOCs for further strengthening the protection.
2. A domain leads to ransomware that has just recently emerged
A monitoring system notifies the SOC team of a suspicious domain name apple[-]online[.]shop. On querying the domain in TI Lookup, it becomes clear that the domain belongs to Interlock ransomware infrastructure.
Sandbox users have marked it as malicious even before public reports on Interlock appeared. The other thing that is obvious in a glance on the tasks list — Interlock is still active and dangerous.
3. Mutex triage: separate the sheep from the goats
Mutex objects are employed to manage shared resources both by malicious and legitimate software, thus mutexes found in the network traffic tend to generate false positive alerts.
Benign applications can use mutexes with the same names as malware samples. Considering all this, TI Lookup can provide valuable data on whether a mutex is linked to known incidents, attacks, or groups.
Let us take for example a mutex with such generic name as PackageManager. Can it mark something dangerous?
Yes it can.
A search by mutex name shows that in recent months it accompanies BugSleep — a backdoor employed by MuddyWater APT group.
Further research with the assistance of TI Lookup and Interactive Sandbox allows to understand the malware’s behavior as well as APT’s scope and TTPs and prioritize the associated alerts as well as orchestrate the preemptive measures and initiate employee training.
Mutexes can also stop being reliable indicators of compromise when certain malware becomes obsolete or gets modified. Up-to-date mutex assessment and prioritization helps avoid false positive signals.
Conclusion: Alert Triage as Key to Efficient Business Security
Alert triage is critical for an effective SOC, and threat intelligence supercharges it by providing the necessary context, automation, and prioritization to focus on real threats. Such solutions as ANY.RUN’s Threat Intelligence Lookup enhance both the speed and accuracy of responses to security incidents.
Get 50 free TI Lookup requests to investigate real world cyber threats
All of this is vitally important for achieving both tactical and strategic business goals: operational efficiency, financial stability, brand strength, beneficial investor relations, and compliance. A proactive approach, fast incident response and mitigation, smart resource allocation are what alert triage via threat intelligence helps achieve.