What is Social Engineering? How Does it Work?
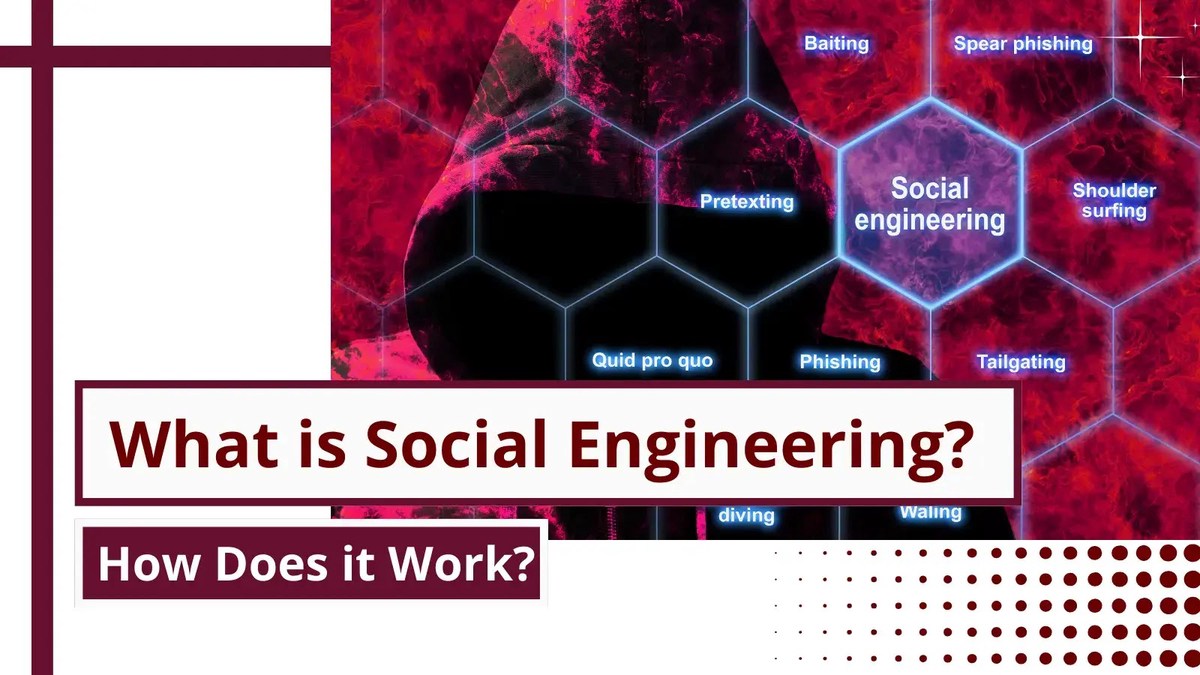
Cyberattacks often use social engineering to trick people into disclosing confidential information. Instead of hacking, it exploits human psychology. An attacker first gathers information about their target to determine their behavior and vulnerabilities.
After gathering this information, the attacker approaches the target as a trusted person or authority figure. By using their trust and authority, the attacker tricks the victim into acting or giving crucial information.
This could involve fooling someone into clicking a harmful link, sharing passwords, or accessing prohibited areas.
Cybercriminals utilize social engineering because it exploits human nature, such as the urge to help or obey authority figures.
Table of Contents
Social Engineering Attack Types
FAQ
1.What is the example of social engineering?
Human mistake is used in social engineering to steal private information, access, or goods. Scammers sometimes imitate trusted figures like bank employees or IT staff to get confidential information.
They may contact or email a victim, requesting passwords or social security numbers to resolve a problem. The fraudster wants to get the victim to skip security.
Phishing emails that impersonate legitimate websites to steal login credentials, baiting scenarios where a USB drive with malware is left in a visible spot, and pretexting use manufactured scenarios or identities to get someone to reveal information.
2. What are the four types of social engineering?
Phishing, pretexting, baiting, and tailgating are the main social engineering methods. Phishing uses fraudulent emails to steal personal information.
Pretexting is creating a story or identity to get someone to reveal information. Baiting uses curiosity or avarice to breach security, like a malware-infected USB device left in public.
Finally, tailgating includes an unauthorized person following an authorized person into a secure place, frequently using the social convention of keeping doors open.
3. What is the basic form of social engineering?
Phishing is the most standard social engineering method. Phishing includes sending fake emails from trusted sources.
Tricking people into exposing passwords, credit card numbers, and other personal information is the purpose.
Due to haste or anxiety, these communications often encourage recipients to act fast without checking. Cybercriminals use phishing to exploit human vulnerabilities because of its simplicity and efficiency.
What is Social Engineering?
Cybercriminals who enjoy preying on people’s weaknesses use social engineering as a technique.
The act of social engineering involves various techniques, all of which involve the manipulation of human psychology.
Threat actors rely especially on social engineering to easily gain sensitive information from victims.
A social engineering attack depends on building trust with the victim so that he never suspects giving out his or her personal information, such as phone numbers, passwords, social security numbers, etc.,
This technique is proven to have been the most successful when it comes to hacking into an organization’s network.
Hackers can disguise themselves as an IT audit person or an external network administrator and easily gain access inside a building without suspicion.
Once they are inside an organization, they use various other social engineering techniques to compromise their network.
One of the greatest weaknesses an organization can possess is the lack of information security knowledge among its employees.
This lack of knowledge in cybersecurity gives hackers a great advantage in performing attacks that cause data breaches in the organization.
Social Engineering Attack Types
Threat actors can use a variety of social engineering attacks. Some of them are,
1. Phishing
2. Vishing
3. Spoofing
4. Tailgating
5. Quid pro quo
6. Baiting
1. Phishing
Phishing is the most simple and effective attack a hacker can use to steal credentials like usernames, passwords, social security numbers, organization secrets, or credit card details.
Sometimes phishing is also used to spread malware inside a network. Phishing is a common form of social engineering in which attackers pretend to be trustworthy organizations in digital communication to get people to give them sensitive information like login credentials or credit card numbers.
Most of the time, this is done by sending emails or messages that look like they came from real places, like banks, service providers, or well-known businesses.
People who get these messages are often scared or feel like they need to act quickly because of them.
Most of the time, they have a link in them that takes the receiver to a fake website that looks a lot like a real one and asks for personal information.
The information gathered is then used for illegal activities like identity theft or cash transactions that aren’t allowed. Phishing attacks depend on the victim’s trust and lack of knowledge, so learning about these types of scams and being alert are very important.
In general, Phishing involves Social engineering as well as Spoofing.
2. Vishing
Vishing, which stands for “voice phishing,” is a type of social engineering in which scammers call people and try to get them to give up personal, financial, or security information.
Vishing is different from regular phishing, which uses email or web messages. Instead, it uses phone calls.
Vishing is similar to phishing, which involves calling the victim and pretending to be a legitimate caller.
Once the victim believes without suspicion, it will be easy for the hacker to gain sensitive information such as network structure, employee details, company account details, etc.,
3. Spoofing
Spoofing is a type of attack where “what we see will look like it, but it is not”.
Spoofing is when someone pretends to be a real company in an email to trick people and get into their information or systems without permission.
As part of this type of social engineering, different parts of the conversation are faked to make the victim think they are talking to a real person.
In terms of cybersecurity, spoofing is nothing but disguising as a legitimate source to gain sensitive information or gain access to something.
An attacker can trick us into believing that he is from the source by spoofing.
4. Tailgating
Tailgating or piggybacking, is a technique used by threat actors to enter an organization’s building.
Tailgating, which is also called “piggybacking,” is a type of social engineering attack in which someone who isn’t supposed to be there gets into a limited area by walking right behind someone who is.
This strategy takes advantage of the social norm of holding doors open for other people, especially in places or buildings that are locked down.
During this attack, the threat actors wait for an employee or a person to enter a place where access for outsiders is restricted and follow them inside the building once they use their access cards or access keys to open the door.
5. Quid pro quo
Quid pro quo in Latin means “a favor for a favor”.
In this case, the hacker communicates with an employee of a company and offers them a deal.
either money in exchange for information or anything the employee would wish.
In most cases, money is the main motto.
Hackers communicate with a present employee or an ex-employee and ask to give away sensitive information such as administrator privileges, administrator passwords, network structure, or any other data they require in exchange for the employee’s wish.
Hackers convince the employees to give away the information by making a personal deal with them.
Because an employee intentionally gave away the information, this is one of the most serious threats to an organization.
6. Baiting
As the word describes, hackers create baits such as USB flash drives, CD-ROMs, floppy disks, or Card readers.
They create folders inside the devices, such as projects and revised payrolls of the organization, and drop them in sensitive areas (elevators, restrooms, cafeterias, or parking lots) where employees would usually keep them.
Once an employee picks up and inserts the USB into their computer, the script inside the device runs and gives full control to the hackers. This method of social engineering is called baiting.
Also Read:
What is a Dictionary Attack? How the Attack Works and How to Prevent the Dictionary Attack
What is Keylogger? How does it work?