WordPress Plugin Vulnerability Exposes Sites to Critical File Inclusion Attacks

A severe security vulnerability has been discovered in the popular InstaWP Connect WordPress plugin, potentially exposing thousands of websites to remote attacks.
Security researchers at Wordfence identified and reported the critical flaw (CVE-2025-2636), which allows unauthenticated attackers to execute arbitrary code on affected websites.
Website administrators are urged to update immediately as the vulnerability received a CVSS score of 9.8, the highest severity rating possible.
InstaWP Connect Plugin LFI Vulnerability
The vulnerability affects all versions of the InstaWP Connect plugin up to and including 0.1.0.85.
This Local File Inclusion (LFI) flaw exists in the plugin’s database management functionality and can be exploited via the instawp-database-manager parameter.
The technical classification is CWE-73: Improper Limitation of a Pathname to a Restricted Directory (‘Path Traversal’).
InstaWP Connect is a popular WordPress staging and migration plugin that enables users to create one-click staging environments and perform site migrations.
The plugin works as a companion tool for InstaWP, allowing users to connect existing WordPress sites to the InstaWP platform for staging, development, and testing purposes.
Security researcher Cheng Liu discovered that the plugin fails to properly validate user input before passing it to PHP, including functions.
A malicious actor could exploit this vulnerability using a simple HTTP request structure:
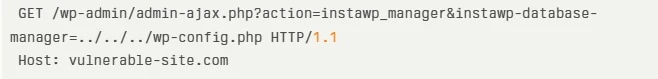
This request could allow attackers to include and execute arbitrary files on the server without authentication. The exploit vector is particularly dangerous because:
- It requires no user authentication
- It can be executed remotely
- It potentially allows for complete server compromise
The summary of the vulnerability is given below:
| Risk Factors | Details |
| Affected Products | InstaWP Connect Plugin for WordPress (versions <= 0.1.0.85) |
| Impact | – Include and execute arbitrary PHP files- Bypass access controls- Obtain sensitive data- Achieve code execution |
| Exploit Prerequisites | No authentication required; remote exploitation possible |
| CVSS 3.1 Score | 9.8 (Critical) |
Impact on WordPress Sites
The vulnerability allows attackers to bypass access controls, obtain sensitive data, including database credentials, and achieve code execution.
In scenarios where image uploads or other “safe” file types are permitted, attackers could upload malicious PHP code disguised as legitimate files and then use the LFI vulnerability to execute them.
According to VulDB intelligence, the potential exploit price for this vulnerability is estimated between $0-$5,000, indicating its relative ease of exploitation.
The CVSS Vector CVSS:3.1 confirms that the attack vector is network-accessible with low complexity and requires no privileges or user interaction.
Website administrators running InstaWP Connect should immediately update to version 0.1.0.86 or newer, which contains a patch for this vulnerability.
If immediate updating is not possible, temporarily deactivating the plugin is recommended until an update can be applied.
This vulnerability follows previous security issues discovered in earlier versions of InstaWP Connect, including authentication bypass vulnerabilities in versions 0.1.0.44 and 0.1.0.38. It highlights the importance of maintaining up-to-date plugin installations.
WordPress security experts emphasize that this type of vulnerability is particularly dangerous because it can be exploited by completely unauthenticated users, potentially leading to full website compromise.
Site owners are also encouraged to implement a Web Application Firewall (WAF) solution as an additional layer of protection against similar vulnerabilities.
Equip your team with real-time threat analysis With ANY.RUN’s interactive cloud sandbox -> Try 14-day Free Trial